FACTS
At the end of 2013, changes were made to the “Wassenaar Arrangement” (WA) (on the Export Control for Conventional Arms and Dual-Use of Goods and Technologies) including references to “zero days”, computer exploits and other software categories (e.g. “intrusion software”) under its controlled exports. These changes took place after the U.S. government allegedly purchased “zero days” computer security vulnerabilities for the National Security Agency (NSA)’s hacking team. Recent additions to the WA are aimed at controlling the spread of exploits and network surveillance tools from repressive regimes and other malicious international actors.
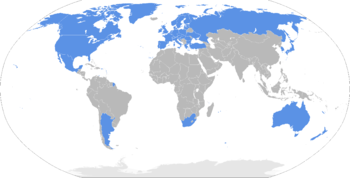
The Wassenaar Arrangement was formed by 41 countries including the US. It was established in 1996 to enhance national and international security standards, by promoting transparency, harmonising national export controls and establishing responsibility for the transfer of conventional arms, dual-use goods and technologies. The Arrangement does not constitute a binding legal measure for its members. On the contrary, its enforcement into the legal framework should be taken in accordance with national legislation and on a basis of national legislative discretion. In other words, WA facilitates information sharing between members and serves principally as consultation body on national export policies and restrictions on export licenses.
The latest changes to the WA relate to: Intrusion software (WA doc at 212) and IP network surveillance systems (WA doc at 81).
REACTIONS
The changes aroused various responses from the WA’s states, business companies and NGOs.
WA’s secretariat stressed its satisfaction with the progress made on the systematic review of intelligence gathering tools and Internet Protocol network surveillance systems. As declared in its official statement, these tools “under certain conditions, may be detrimental to international and regional security and stability”.
From a business point of view, changes to WA influenced some companies (such as VUPEN) to restrict exploit sales and exclude countries subject to European Union (EU) restrictions or embargoes by the US or the United Nations.
NGOs and human rights defenders stimulated the WA’s changes too. They are asking to pay attention to the civil society perspective on dual-use goods and technologies (see open letter published before WA’s plenary meeting). These organisations underlined the increase use of surveillance technologies in repressive regimes around the world. To give a real example, countries under political regimes are banning access to social media and using sophisticated technologies imported from Europe to block and catch dissident people (e.g. Syria, Saudi Arabia and Vietnam).
KEY QUESTIONS
These changes are related to controls on exports and more generally to the regulation of computer vulnerabilities market. According to WA’s reactions already mentioned, we can see how exploits can be considered as knowledge or as ‘weaponized’ tool. In other words, we have to deal with the following issue: on the one hand, exploits can be treated as know-how alike an example of licit scientific/technical application, for instance, a peculiar vulnerability of one precise software or system. On the other hand, exploits are interpreted as weapon tools and meanwhile compared to written codes to exploit that vulnerability.
The recent implementation of the agreement leaves some blurred definitions and unclear applications. Many questions must be answered to fill the gap between the Arrangement and its practical enforcement; for instance: how do we reach a balance between the need for transparency/harmonization to control dangerous exploits export and a free exchange of knowledge of vulnerabilities?
Some scholars have already highlighted extensive harmful effects on computer security research and defensive software. They proposed a different formulation to achieve the Wassenaar Arrangement’s benefits without causing chilling effects.
Also EU politicians, like Marietje Schaake (see also Invitation to security researchers to make suggestions on export controls), pointed out that strengthening export controls of dual use technology should be focal point of EU policy. In this respect, the European Commission has recently adopted a Communication, with some important conclusions on the dual-use items and export controls such as first step for a future legislative proposal. Generally, the Communication is focused on assessing the interface between the dangers of technologies and the way in which controlling European exports may adversely impact human rights as well as business. With a focus on its goals, the EU Commission aims to “an updated EU approach and regulatory framework will reinforce the security and integrity of supply chain”. This target should be reached through more risks information sharing amongst EU members and coordination between licensing and other authorities. Last but not least, the role of the private sector and closer international cooperation are both key elements for fruitful improvements (see the Communication)
A very last and controversial update to the Arrangement was published on the 20th May 2015 by the U.S. Department of Commerce’s Bureau of Industry and Security (BIS). Specifically, the BIS proposal would add to the list of controlled technology the following items:
- “Systems, equipment, components and software specially designed for the generation, operation or delivery of, or communication with, intrusion software include network penetration testing products that use intrusion software to identify vulnerabilities of computers and network-capable devices”.
- “Technology for the development of intrusion software includes proprietary research on the vulnerabilities and exploitation of computers and network-capable devices”.
As we can see from the official document, it was also implemented the enforcement of a license requirement for export and transfer of such cyber security items to all destinations except Canada. The most impressive aspect about last updates concerns the approximation about terminology used as well as examples considered into the category of “intrusion software”. To put it differently, there is a significant risk for a massive banning into the worldwide market about common legitimate tools also used within the security and research contests. The strangest paradox is that also widely-used tools (e.g. Google Chrome) could be affected by the export control with the same modality for encryption items (see board set of controls).
Nevertheless, there is still possibility to intervene in order to change, or almost modify, these new rules with comments until the 20th July. The feedback has already begun.
We will stay on the lookout for upcoming developments!
Marco Mendola
Tech & Law Center Fellow