President Barack Obama has officially declared a cyber security emergency. On 1 April 2015, the U.S. Administration published the New Executive Order “Blocking the Property of Certain Persons Engaging in Significant Malicious Cyber-Enabled Activities”. This authorizes the Treasury Secretary General and the Attorney General to apply tough sanctions against international actors engaged in cyber-enabled activities that threaten the national security or the economic health of the United States.
According to the White House Press Office’s declaration, the Executive Order targets actions that are: “compromising critical infrastructure; misappropriating funds or economic resources, trade secrets, personal identifiers, or financial information for commercial or competitive advantage or private financial gain; knowingly receiving or using trade secrets that were stolen by cyber-enabled means for commercial or competitive advantage or private financial gain; disrupting the availability of a computer or network of computers; and attempting, assisting or providing material support for any of the above activities”. However, when taking a closer look at the Executive Order, it is not easy to interpret the meaning of “cyber-enabled” activities properly. According to the Order, “cyber-enabled” activities must have the purpose or the effect of:
- harming or significantly compromising the provision of services by an entity in a critical infrastructure sector;
- causing significant disruption to the availability of a computer or network of computers (for example, through a denial of service attack);
- causing significant misappropriation of funds or economic resources, trade secrets, personal identifiers, or financial information for commercial or competitive advantage or private financial gain;
- knowingly receiving or using trade secrets misappropriated through cyber-enabled means for commercial or competitive advantage or private financial gain (for example, a corporation that knowingly profits from stolen trade secrets); or
- materially assisting, sponsoring, or providing financial, material, or technological support for any of the above activities.
Given the open-ended nature of these provisions, it is unclear how this order should be considered.
On one hand, the Executive Order constitutes an effective tool in combating economy and national security threats. (Initially, this seems strictly related to the attack on Sony Pictures in January 2015, where President Obama imposed sanctions on North Korea, but official statements by the Government expressly reject this political interpretation).
On the other hand, this legal measure could represent a threat in itself for digital society in the long run. As pointed out by Nadia Kayyali and Kurt Opshal of the Electronic Frontier Foundation (EFF), the Orders’ “chilling effect” on cyber security research is a serious threat. Instead of encouraging critical security research into vulnerabilities, this measure could practically discourage any interest on it. Furthermore, determining which individuals or entities are targeted by these sanctions is not clear and the scope of the Order appears extremely vague.
Analysing the Executive Order, we can deduce three main areas of focus:
- Defining “malicious”: according to Mr. John Smith of Office of Foreign Assets Control (OFAC): “how we define or characterize what ‘malicious’ would be is really with respect to the harms that you see in sections 1(a) and then A through D of the executive order”. There is no doubt that the meaning of malicious does not appear so definite from a legal perspective. A broader reference to all examples quoted in the Order cannot constitute an appropriate interpretation. It is also possible to envisage a serious risk of future misinterpretations, where targeted facts are indiscriminately included such in a “catch them all” clause.
- Defining “significance”: the Order does not define what “significance” means in great detail. How the U.S. Administration defines this concept will impact how the sanctions are implemented.
- Due Process clause: Essentially, the Executive Order permits enforcement without prior notification to the individual and beyond other guarantees such as the admissibility of evidence. Nevertheless, Mr. Smith specifies that each sanctioned individual has the ability to challenge their designation with OFAC by administrative petition or through a law suit in any federal district of the country. Considering his blurred explanation about OFAC legal procedure, as jurists, we can assist to a quite abnormal application of the due process of law.
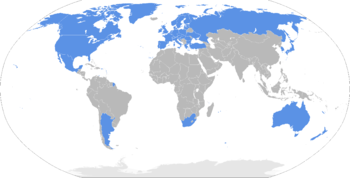
It might seem that these sanctions will not affect individual interests, companies’ businesses and defense activities, as they primarily focus on malicious cyber activities that impact American infrastructure. However, even for us non-American citizens the future implications of the Order are significant. Jurisdiction in cybercrime follows its particular criteria, in which cross-border effects are influencing the Internet ecosystem. These sanctions are also intended to be used against foreign actors outside the jurisdictional reach of the USA if other forms of legal, political or economic mechanism prove to be ineffective.
It is early to evaluate all of the possible consequences that may arise from the passing of this Executive Order. Nonetheless, we have to bear in mind that one of the fundamental principles of cyber security is that unclear laws, wide prosecutorial discretion and draconian punishments are not adequate responses to computer crimes.
Marco Mendola
Tech & Law Center Member
Photo credit: P080709PS-0290 via photopin (license)